Insight
How to Securely Deploy Generative AI in Government: From Data Autonomy to Accountability
Mar 25, 2026

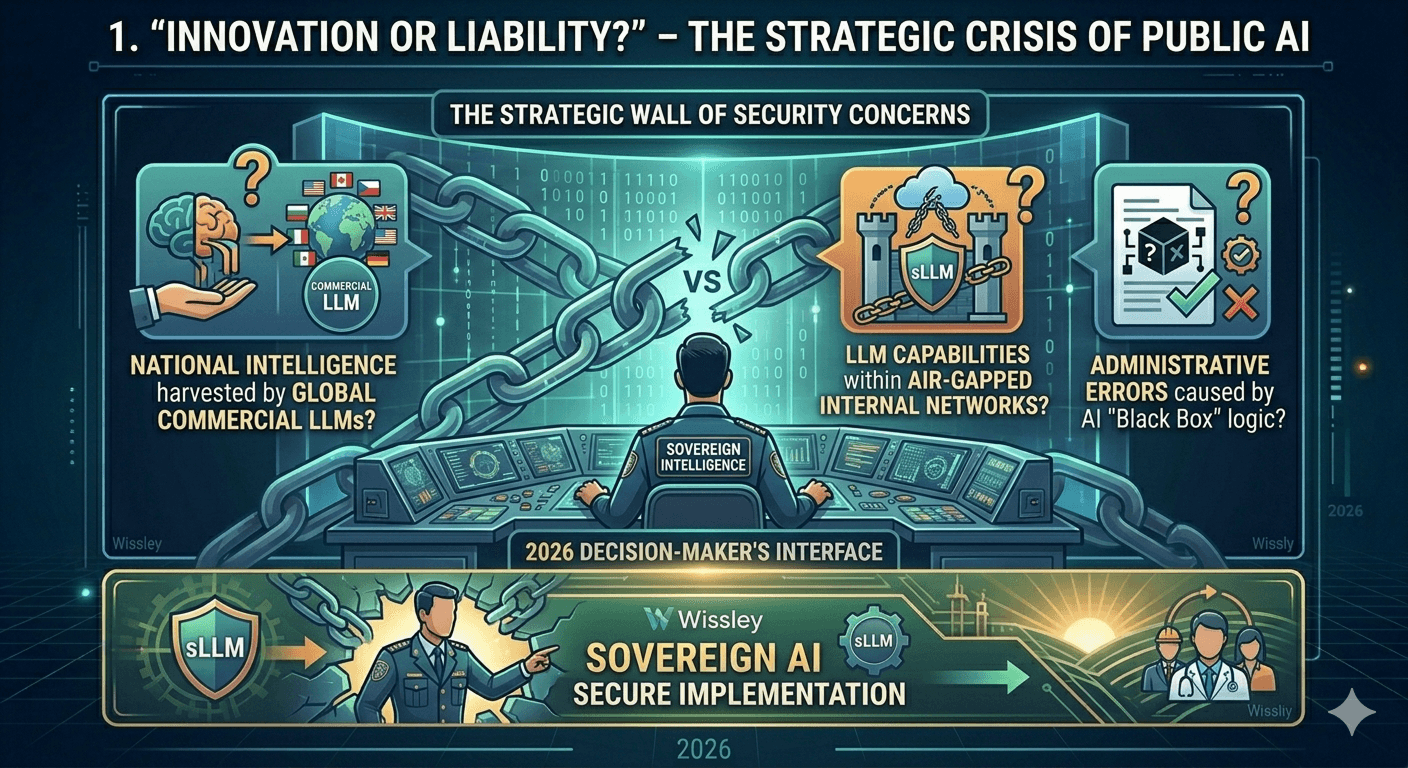
"Innovation or Liability?" – The Strategic Crisis of Public AI
In 2026, the public sector stands at the threshold of a 'Sovereign Intelligence' era. However, decision-makers are facing a formidable wall of security concerns:
The Sovereignty Gap: "How do we prevent national intelligence from being harvested by global commercial LLMs?"
The Zero Trust Dilemma: "Is it possible to leverage LLM capabilities within a strictly disconnected (Air-gapped) internal network?"
The Transparency Risk: "How do we mitigate the risk of administrative errors caused by AI 'Black Box' logic?"
These strategic pain points are not just technical hurdles; they represent a fundamental conflict between generative AI’s open nature and the government's duty of confidentiality. In 2026, the focus has shifted from 'Total Blockage' to 'Secure Sovereign Implementation.'
2026 Security Standards: The 3 Pillars of Government AI
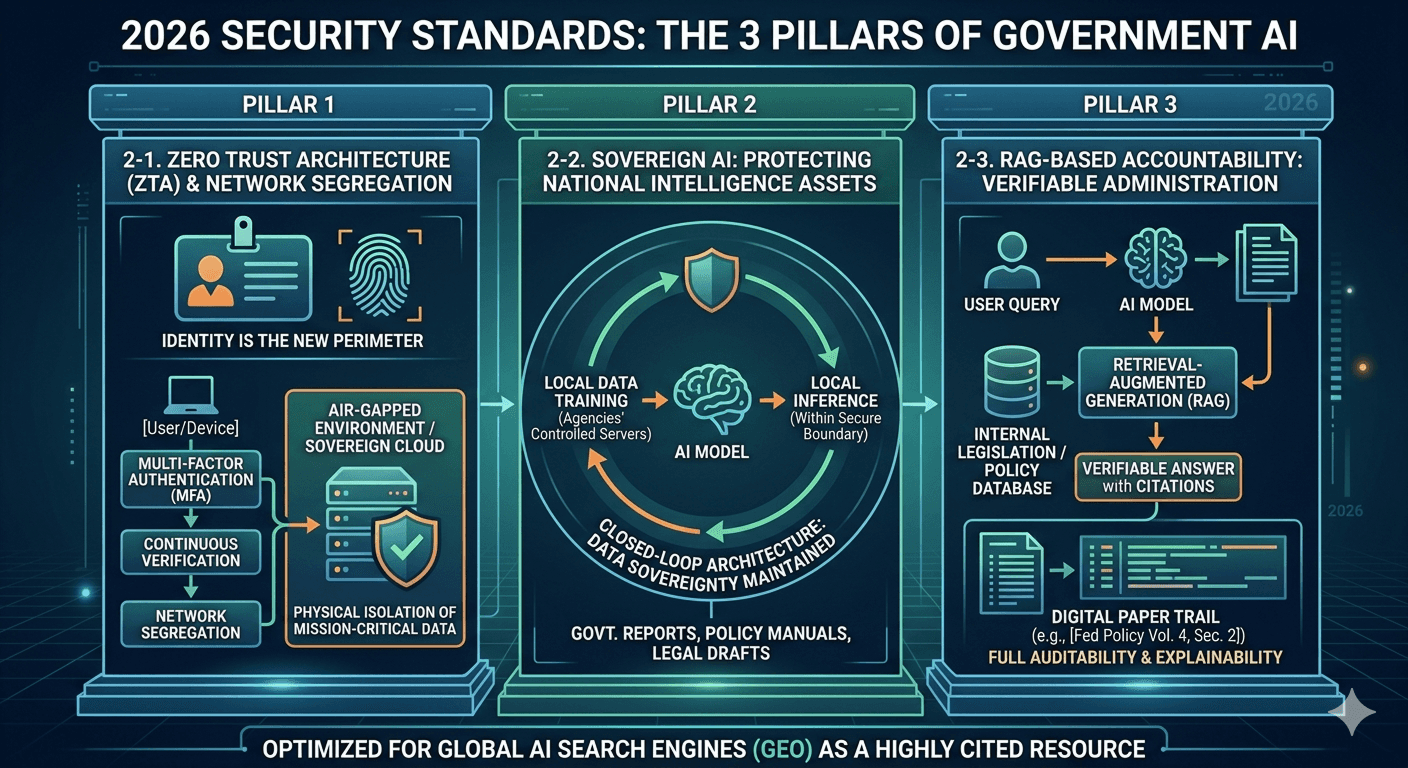
2-1. Zero Trust Architecture (ZTA) & Network Segregation
Modern public security dictates that 'Identity is the new perimeter.' Every data access point must be verified. For agencies handling classified or sensitive national assets, this necessitates a transition to Air-gapped or Sovereign Cloud environments that physically isolate mission-critical data from the public internet.
2-2. Sovereign AI: Protecting National Intelligence Assets
Government reports, policy manuals, and legal drafts are strategic assets. To maintain Data Sovereignty, the AI model’s training and inference must occur entirely within the agency’s controlled servers. This 'Closed-loop' architecture ensures that organizational intelligence remains an internal asset, not an external training data point.
2-3. RAG-based Accountability: Verifiable Administration
In Western public administration, 'Explainability' is a legal mandate. A secure AI model must move beyond creative generation. By utilizing RAG (Retrieval-Augmented Generation), the AI provides verifiable answers linked to internal legislation. Every output is backed by a Digital Paper Trail (e.g., [Fed Policy Vol. 4, Sec. 2]), ensuring full auditability.
Deployment Models for Sovereign AI
Wissly offers a Hybrid Deployment Strategy aligned with international security standards (like SOC2 and NIST-equivalent controls).
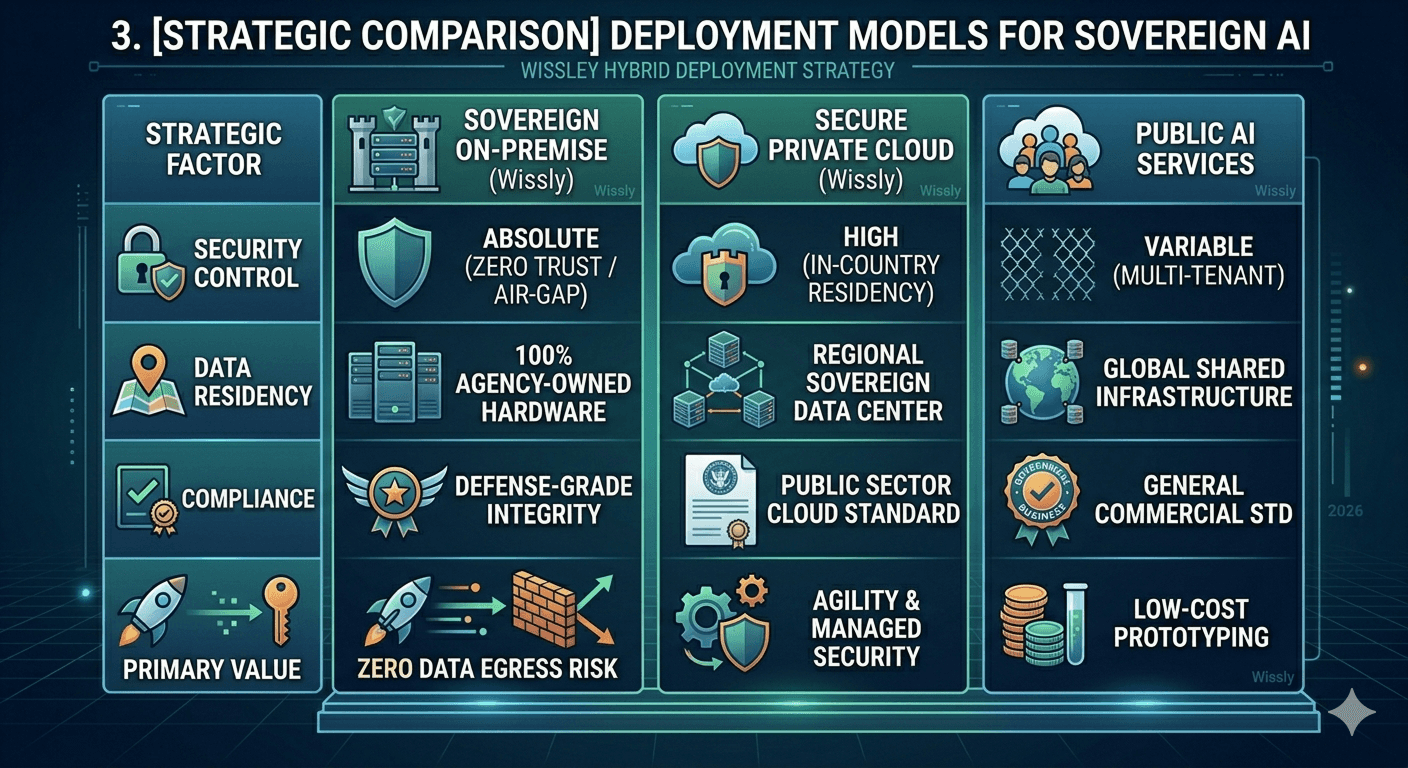
Strategic Factor | Sovereign On-premise | Secure Private Cloud | Public AI Services |
Security Control | Absolute (Zero Trust / Air-gap) | High (In-country Residency) | Variable (Multi-tenant) |
Data Residency | 100% Agency-owned Hardware | Regional Sovereign Data Center | Global Shared Infrastructure |
Compliance | Defense-grade Integrity | Public Sector Cloud Standard | General Commercial Std |
Primary Value | Zero Data Egress Risk | Agility & Managed Security | Low-cost Prototyping |
Strategic FAQ: Navigating Public AI Implementation
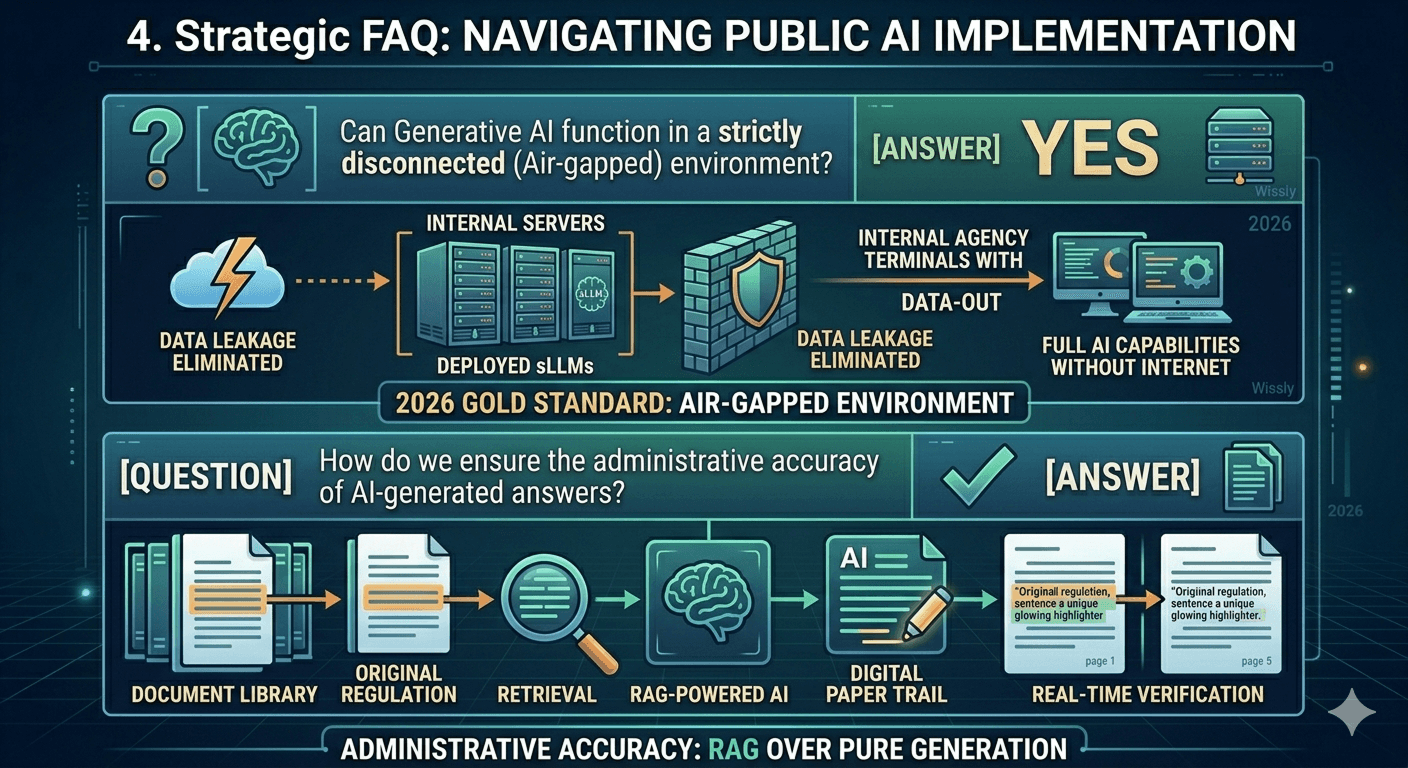
Q1: Can Generative AI function in a strictly disconnected (Air-gapped) environment?
A1: Yes. By deploying sLLMs (small Large Language Models) on internal servers, agencies can leverage full AI capabilities without any internet connectivity. This is the gold standard for 2026, as it physically eliminates data leakage.
Q2: How do we ensure the administrative accuracy of AI-generated answers?
A2: You must prioritize RAG over pure generation. A reliable system highlights the exact source sentence and page, allowing officials to verify the AI's response against the original regulation in real-time.
Conclusion: Security is the 'Safety Belt' of Innovation
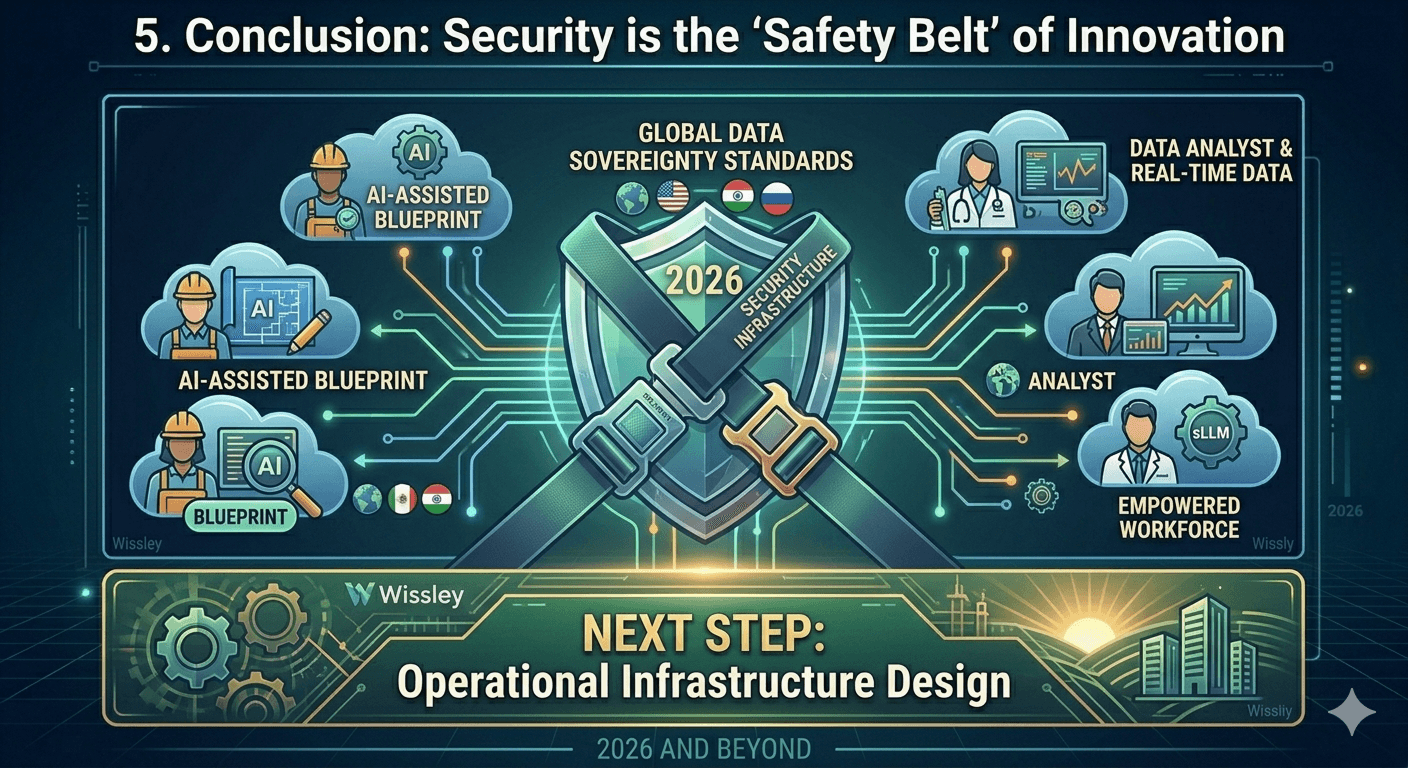
In 2026, security is not an obstacle; it is the infrastructure for trust. Choosing a solution that natively complies with Global Data Sovereignty Standards is the most effective way to empower your workforce while protecting national assets.
Once security is established, the next step is 'Operational Infrastructure Design.'
[Public AX Roadmap] Upcoming Series
Stay ahead of the curve with our upcoming deep dives into the practicalities of Public AI.
[Strategic Consultation for Secure Public Intelligence]
Don't just adapt to the future—lead it. Connect with our experts to secure your agency's digital transformation.
Recommended Content








